Did you know that more than 4.6 billion people on the planet are expected to use email by 2025? That’s more than half of the world’s population, and they are expected to send a staggering 376.4 billion emails every day in that same year. That widespread use is why email remains a preferred method of communication for nonprofits of all types. However, email’s omnipresence has permitted cybercriminals to get much better at exploiting it and developing new and creative ways to scam users out of their personal information and jeopardize the security of nonprofit networks.
We strongly believe that in addition to having a strong IT team implement state-of-the-art cybersecurity measures, the strongest defense is education. One of the easiest ways you can boost your organization’s security is to teach your employees and volunteers to read links. Doing so effectively will reduce the likelihood of a successful phishing scam that arrives in their inboxes.
Since sketchy links are so common, many people already avoid clicking on links from people they don’t know. However, many phishing scams now look as if they are coming from legitimate email addresses you know and trust, so learning how to read URLs can keep you safe no matter the source.
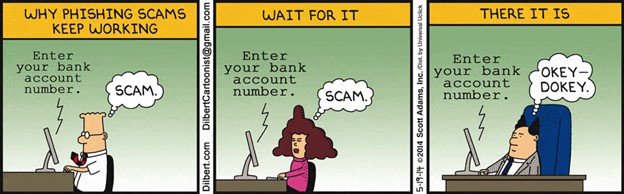
Believe your team won’t fall for scams like this? Dilbert shows us why they still work…
It’s a numbers game. If they send enough emails, eventually one person will click. Here’s how to make sure that one person who does, does not work for you – and isn’t you!
#1 – Spelling Errors
Let’s face it, due to the sheer volume of emails we all get, we often skim them without thoroughly reading them. That leads to one of the most common ways cybercriminals sneak past us in phishing scams – misspelled domains. Look at the URLs below and see if you can spot the errors.
- crossthedivdie.com
- www.rncdonalds.com
- www.linked1n.com
- www.spotfy.com
1 – Scrambled Letters
When letters inside long words are scrambled, our brains typically make the correction without us noticing the error.
2 – Letter Combinations
This one is falling off in popularity as more people have varied fonts on their browsers, but it’s still used to combine two letters to look like another. In this case, the “r” and the “n” look a lot like the letter “m.”
3 – Swapping numbers
No doubt the “o” vs. “0” issue or in this case, the “1” vs. “l” has tripped us all up at some point. It’s also a popular way used to mask a problem URL.
4 – AWOL Letters
While this is less effective on short URLs, skipping a letter in a longer domain name can be very difficult to spot.
#2 – Mixed Up Domains
As potential victims get better at spotting the mix-ups, we noted above, cybercriminals have resorted to masking the top-level domain, tricking victims into believing they are going somewhere they are not. To determine the top-level domain, follow these two rules:
- If there aren’t any single forward-slash characters in the URL (/), then read the top-level domain from left to right.

- If there are single forward-slash characters in the URL (/), find the one that is farthest from the right. Starting from that forward slash, read the top-level domain from right to left.

Since we are only attempting to find single forward slashes in the URL, the double forward slash in https:// does not apply.
You try it. Look at the URLs below and see if you can determine which are genuine domains, and which might be dangerous:
- www.business.facebook.com/login
- http://activate.facebook.fblogins.net/8676408?login.php
- www.facebook.login.com/account
- www.facebook.com/ads/library/?active_status=all&ad_type=political_and_issue_ads&country=US&media_type=all
1 – Good!
The forward slash is between login and com, so the top-level domain is facebook.com
2 – Bad.
The forward slash is between 8675309 and net, so the top-level domain is fblogins.net, not Facebook.
3- Bad.
The forward slash is between com and account, so the top-level domain is login.com, not Facebook.
4 – Good!
The forward slash is between ads and com, so the top-level domain is Facebook.com. We’ll explain the meaning of the rest of that URL in a moment.
#3 – Short Links
Short links are fairly common on social media platforms like Instagram and email because they make it much simpler to physically type in when you can’t simply click through. Some of the most common resources for creating a short URL are Bitly, Rebrandly, and TinyURL. Another reason that marketers use short links is to reduce character counts on social media posts. Since they are now so common, cybercriminals have started to use them as well. Here’s an example of a short link: https://tinyurl.com/3333anv8.
So how do you know a short link is safe? Fortunately, when it comes to ads, many social media carefully scan linked websites for authenticity, quality, and relevance to the ad itself. So, you can be reasonably sure a link in an ad is safe.
When it comes to email, it pays to be more suspicious to prevent phishing scams. We recommend copying and pasting the short link into one of several online tools that will expand it for you, then you can follow the steps above to determine if it is safe. Here are some of the more popular sites for expanding short links:
UTMs & Tracking
Have you ever wondered what that mess of random words and numbers at the end of a link means? They are called UTMs, which stand for Urchin Tracking Module or Urchin Traffic Monitor. The name is derived from Urchin Tracker, which is the original web analytics software that predates Google Analytics. In essence, these set parameters allow marketers to track the information they are seeking about people who go to the page.
Here’s what one might look like:
https://www.crossthedivide.com/insight/cybersecurity-in-2021-a-look-forward/?utm_source=blog&utm_medium=reading_urls&utm_campaign=cybersecurity_guide&utm_term=example_link&utm_content=reading_utms
If you follow the single forward-slash method that we talked about above, you can sort through this complexity to what matters. In this case, you can see that the top-level domain is Crossthedividecom, so you know you are safe. Here’s what the rest of that chain means:
Everything after the question mark (…a-look-forward/?utm…) is used for tracking purposes. It helps organizations understand where their website traffic is coming from. In this example, here’s the information a company would gather:
- Campaign Source: Blog
- Campaign Medium: Reading URLs
- Campaign Name: Cybersecurity Guide
- Campaign Content: Reading UTMs
So, while it matters to marketers who need to rely on tracking data to prove that their campaigns are working, it doesn’t matter to the end user. Although UTMs can be used to better hide sketchy URLs, following the best practices we talked about earlier can help you avoid them, regardless of the length or complexity.
Unfortunately, even once you understand URLs, there are other methods out there such as “onMouseOver” event triggers, Punycode DNS registrations, href attributes, data URLs, and more that you can fall victim to. The large variety of cyberattacks is why you should always layer your knowledge of common scam approaches with other methods of cybersecurity. That way, if you or an employee clicks on a shady link, your additional layers of protection such as antivirus software, secure routers and more can keep you safe. Want expert help on keeping your systems safe? Reach out to us.